How to check if your Citrix Netscaler has been compromised by attackers

If you missed our blog post last week, there is a very serious exploit affecting Citrix Netscalers. The exploit allows for attackers to gain access to corporate resources without compromising existing user accounts. Basically running unauthorized code anonymously. In the previous blog post, we listed out the mitigation method recommended by Citrix. It is a series of CLI commands you can run on the Netscalers.
Since the writing of the first blog posts, public exploit code has been made available and researchers have been reporting attacks on honey pot environments.
Here is how you can check to see if your Netscaler has been compromised.
You can run the following commands:
shell ls /netscaler/portal/templates/*.xml
shell ls /var/tmp/netscaler/portal/templates
shell ls /var/vpn/bookmark/*.xml
These commands were taken from the write up on Nerdscaler.com. You can see an example output of a compromised Netscaler below.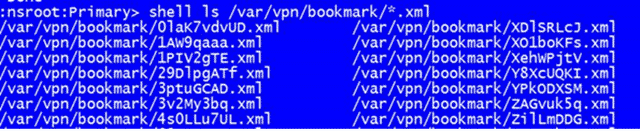
If you think you have been compromised, the remediation steps are lengthy and thorough and listed out in the article above.
Citrix and FireEye have also released an Open Source script to assist in troubleshooting the Netscalers.
New Tool: Check if your Citrix Netscaler have been Compromised
Stay safe out there!
–Carlo

