See inside Registry.pol with the Pol2Reg utility

Here is another great utility for the Windows administrator’s Toolbelt, written and shared by Jacques Bensimon.
Okay, this may be a solution in search of a problem, but the new utility Pol2Reg.exe lets you create an import-ready Unicode .reg file that reflects the contents of any Registry policy .pol file (typically named Registry.pol when located in the Machine or User subfolder of a domain Group Policy Object or of the local Windows\System32\GroupPolicy folder). Actually, I can think of a couple of uses for this utility:
- Transferring Registry policies from a GPO or local policy to an off-network or off-domain machine, or to Home editions of Windows (which don’t support policy application via the normal mechanism).
- View the policies contained in a specific Registry policy file when the Policy Editor is unavailable to you.
- Seeing the actual Registry keys and values created (or deleted) by a given Registry policy file without having to wade through ADM/ADMX policy templates.
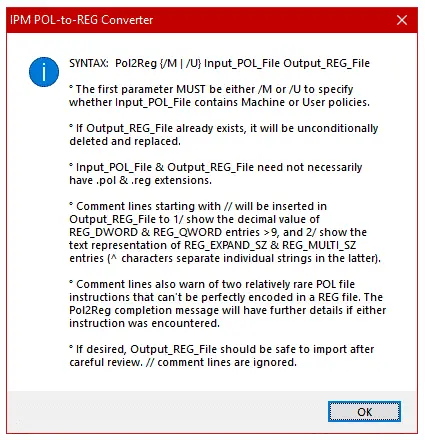
Running the utility without parameters (or with invalid parameters) will display the following syntax help and usage notes:
Notes:
- The POL file format is an unusual combination of binary data and Unicode text, and is reasonably well documented here, minor errors aside. Pol2Reg is based on this specification and on other clarifying documents.
- As stated in the above screenshot, the utility’s first parameter must be the switch /M or /U to specify whether the input POL file contain Machine or User policies. This is because a POL file does not contain that information – it is inferred from its folder location when being applied by the policy engine. The switch dictates whether the output REG file will target HKEY_LOCAL_MACHINE or HKEY_CURRENT_USER.
- Comments (lines starting with //) are automatically added to the output REG file to provide the decimal equivalent of REG_DWORD and REG_QWORD entries greater than 9, and the text representation of binary-encoded REG_EXPAND_SZ and REG_MULTI_SZ entries. Don’t you wish Regedit did that for you when exporting to a REG file?
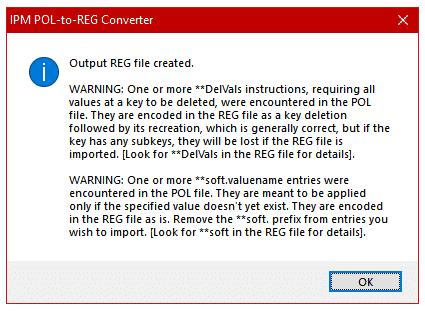
- There are two actions potentially specified in a POL file (the second one so rare that I’ve yet to encounter it in the wild) that can’t be perfectly captured in a REG file: 1) a **DelVals instruction requires that all existing values directly under a key be deleted before continuing – this is encoded in the output REG file as a key deletion followed immediately by a key recreation (since a static REG file can’t know what values may already exist under any given key). This works well in practice, but although unusual for the sort of value lists targeted by **DelVals, there’s always the possibility that the specified key also had subkeys, in which case the subkeys would be lost in the process. 2) some value names may apparently (in theory) be specified with a **soft. prefix, for example “**soft.ValueName” – this requires the policy engine to only create the value ValueName if it doesn’t already exist at the specified key (“soft creation”). Pol2Reg leaves the **soft. prefix as is in the output REG file to avoid overwriting an existing value if the REG file were to be imported. If either one of these special instructions is encountered in the input POL file, the Pol2Reg completion message will include an appropriate warning, as shown in the screenshot below (which in this case includes both possible warnings):
- For maximum platform compatibility, Pol2Reg is compiled as a 32-bit executable. If you wish to directly target a POL file under System32 on a 64-bit system without first copying it elsewhere, use the “SysNative” trick described here, for example:
Pol2Reg /M C:\Windows\SysNative\GroupPolicy\Machine\Registry.pol %Temp%\Machine.reg.
Well, that’s it. Belated Happy Independence Day (also Pol2Reg’s birth day ????) to my fellow Americans!
JB
Follow Jacques Bensimon on Twitter @JacqBens for more great Windows insights and tricks.

